
I like salted caramel and Pringles of salt and vinegar flavour. But yesterday, I heard about ‘salting’ passwords for the first time and learned about them!
I was look forward the month of April because of two reasons:
- The long needed term one school holidays
- The first ever re_B00TCMP on Perth
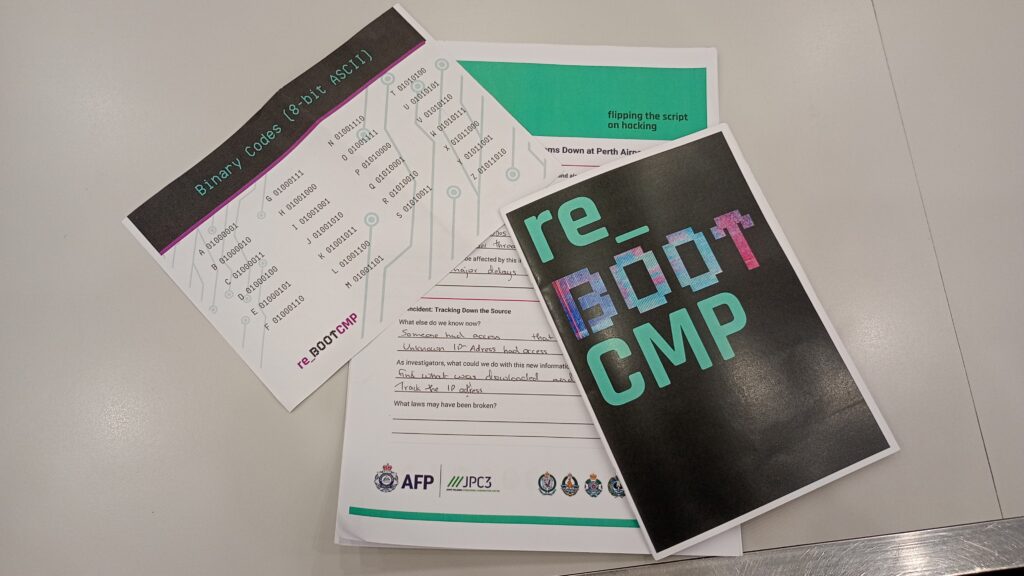
Australian Federal Police (AFP), Joint Policing Cybercrime Coordination Centre (JPC3), and Edith Cowan University conducted the first ever re_B00T CMP in Perth yesterday, which I attended along with 40 passionate high school students. It is a pilot program that encourages students to learn what ethically hacking is, pursue careers in cybersecurity and hone their skills. It felt like a good opportunity to network with similar high school students with an interest in cybersecurity as well as cybersecurity professionals.
I would like to thank my high school teacher Donna Buckley for remembering me and passing the information of this bootcamp along.
So, with excitement and nervousness I was prepared to attend re_B00TCMP at Edith Cowan University.
ECU

During the breaks we sat in the benches near the building facing the pond and sculpture park.

The venue was familiar to me as PECAN+ CTF 2025 was held at the same building as this bootcamp. Saw some familiar faces as soon as I entered — Karina Price and Petra Trinke, whom I have seen from several GPN lessons and PECAN+. I also got to reconnect a friend from school which was very nice.
1. Network Jam
We kicked-off with a network jam session, connecting with each other through fun games of Cyber Taboo and Bingo.
Cyber Taboo was fun because it was words related to cyber security (duh). We made small groups if 10 that competed with each other to guess the most words withing 5 minutes. There was a bowl filled with chits of questions.
The game works by a person taking a chit with a word, they then have to describe the word like what it is for their teammates to guess. Of course they should not say the word, but work around it to give clues that make what the word is obvious. We had really fun ones likes honeypot, salting, hashing etc.
Then we played a fun round of Bingo which helped me connect with others in the room including amazing mentors like Monique Cornall who helped me strike out ‘I built a computer’ while saying she had “just built one last week” (which is really cool).
I was also surprised to learn so much just from the first few hours of the program.
Learnings
From the first session I learnt about…
- Salting and peppering a password
- Rubber ducking a coding problem!
- Zero Day
- What does a mechanical keyboard mean (aren’t all keyboards ‘mechanical’ well apparently not!)
- TCP vs UDP
- What bricking a device is
2. Keynote with Mark
We got to hear an intriguing story from Mark Blaszczyk about his journey of exploring the rules of the internet.
Growing up before the internet had rules, Mark learned to crack games, explore networks. Around him were others like him: some curious, some chasing status, some going too far. He talked about his first ‘hacking’ being in games on Amiga Action Replay by using it to jump levels and get lives.
He tehn went on to share about how at 15 years old, Mark accidentally logged into a NASA server. and how a week later, police cars surrounded his street. Panicking at the situation he wiped everyting he had done, only to learn they were there for his neighbours! He says how that experience of hiding inside a dog kernel waiting for the police to leave opened his mind to the dangers of going beyond the saefty line.
He talked us through his career as a cybersecurity researcher that studied cybersecurity at TAFE and currently doing bug bounties. It was an amazing eye opening session from him.
Learnings
- Amiga Action Replay
- Bug bounties and Google Issue Tracker
- Ethical hacking
3. Cybercrime Scenes with Police
In this session we got to see behind the scenes of how cybercrime is handled by the AFP police and how cyber investigators work, thanks to Rob Goodall and Lachlan Cameron.
We listened and analysed key evidence of cybersecurity breach by an individual named ‘Jack’ that caused air traffic control communication systems to go offline, causing panic at the Perth Airport.
A part of this assesment was to look at digital exhibits like a Reddit post and Outlook email used for fishing.
It gave us an in depth experience on how cyber investigators work and how strong tech skills can be used for good, like for solving cybercrime cases.
Learnings
- Gathering evdience when a cybercrime happens
- Cybercrime commonwealth laws in Australia (Criminal Code Act 1997)
Lazy_Us Group
Our mission was to navigate through an AFP cybercrime investigation against an organisation named Lazy_Us, a group of tech graduates accused of leaking confidential documents. The program was run using Gauntlet, delivered by Retrospect Labs and Kinetic IT it is a web based cyber security exercise platform designed to help organizations test and practice incident response capabilities.
We were grouped into teams where we had to work together through each exercise to analyse the information provided in each level, to answer the questions given. They had a Linux machine stimulater built within, which we used to look at pdfs, text files etc.
It was also my first time using Wireshark to open a .pcap (packet capture files). We looked at a compromised user’s network traffic, by looking at the ‘recording’ of data packets moving across the network. The questions were mostly at how to filter through the information to find specific files like jpgs that the group had used to display a ‘Lazy_Us Group wallpaper’ on the users device. (To make it manageable for us first time cyber analysis to find the answers, the files were conveniently named ex: Hacked_Wallpaper.jpg)
Thanks to Jason Pang, Divij Bhaw, and Tony C. for helping us along the way, when we were stuck on a problem. Jason patiently helped me learn what a MITRE ATT&CK was. It is a whole dictionary or library of free knowledge base of adversary tactics and techniques that is gathered from real world observations of cyber attacker behaviors. We had questions asking us to identify what type of MITRE ATT&CK was done (ex. Exfiltration Over Web Service, ID: T1567).
Learnings
- What packet capture file is
- How to use Wireshark
- MITRE ATT&CK
Panel Discussion and Breakout Session
It was great to hear from Karina Price, Petra Trinke, Kenneth Tan, and Tony C. in the field of cybersecurity, sharing their pathways, studies, experiences, knowledge, and advice for us students. The breakout session with professionals in Cybersecurity — Riley Grimwood, Monique Cornall, Lana Chevenkova, Blake Dobels, Maggie O’Connell, and Lachlan Cameron — was inspiring.
I’m looking forward to the PECAN+ CTF Challenge 2026 in August. I had so much fun and was happy to have been a part of re_B00TCMP 2026.
